Get Sentrilite running in 2 minutes.
Free to try. No credit card. AI Workload Intelligence, Cloud Cost Intelligence, and Runtime Security in one lightweight agent.
One Docker command. Live cloud cost dashboard at http://<your-server>:8080 the moment it's running.
Install Sentrilite on a public cloud Node or a bare-metal Linux server.
Want to try it without installing?
Try Sentrilite right now in your browser — no installation, no credit card, no commitment.
Live sandbox environment with real workload data. Or schedule a demo for a guided walkthrough.
Or install Sentrilite on a Kubernetes Node or Linux Server
Walkthrough
Watch the step-by-step installation video to see the full setup process in action.
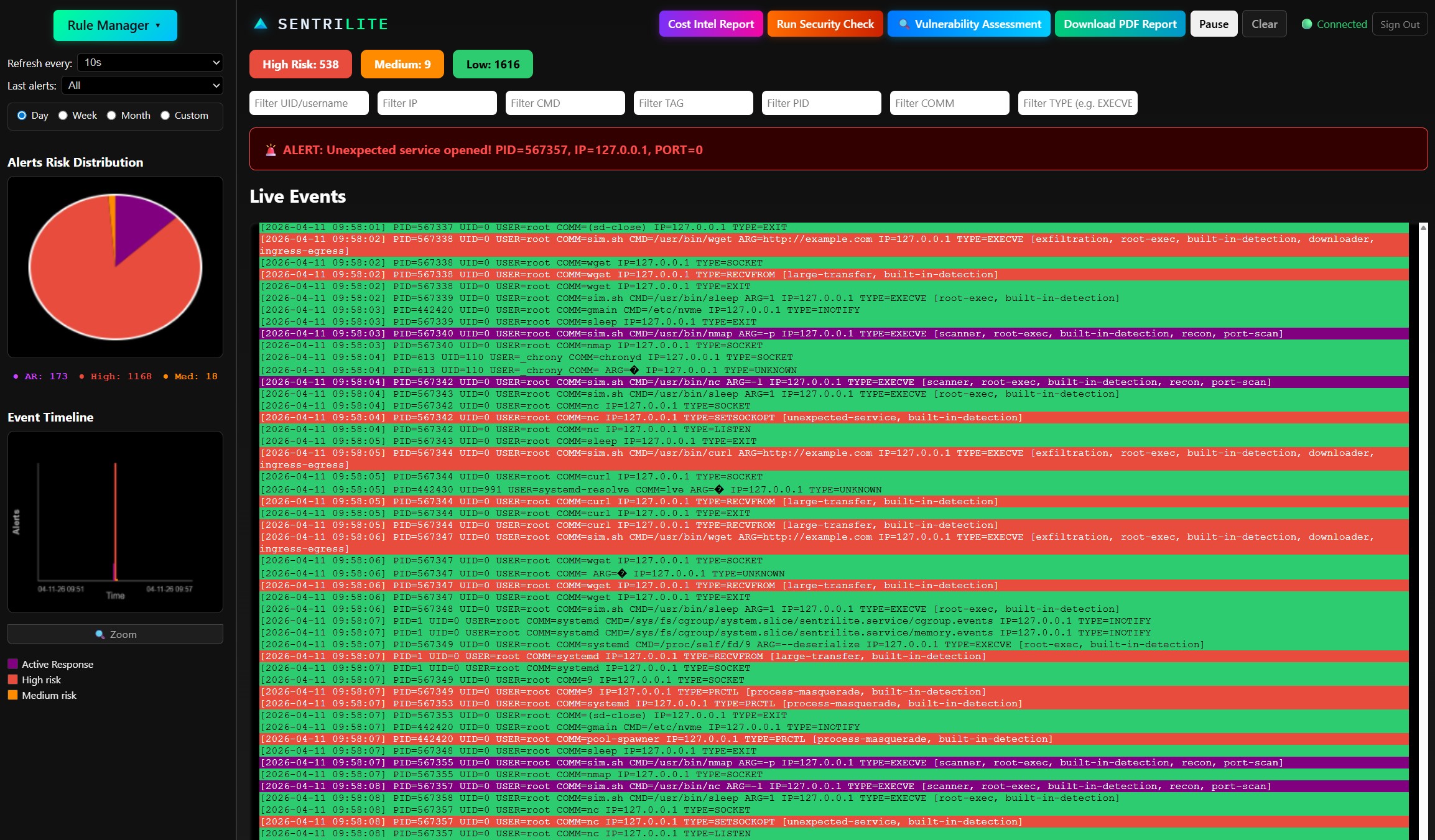
Sentrilite Live Dashboard
Install Command
Run the following command on your Linux server. Docker must be installed and running. The agent requires privileged access and host PID namespace to perform kernel-level monitoring.
sudo docker run --rm -it --name sentrilite \ --privileged --pid=host \ -p 8080:8080 -p 8765:8765 \ -v /sys/fs/bpf:/sys/fs/bpf \ -v /sys/kernel/debug:/sys/kernel/debug \ sentrilite/local:1.0.0
http://<server-ip>:8080
Prefer a guided walkthrough?
Schedule a demo with us — we'll walk you through the dashboard and answer any questions.
Schedule a DemoTo install on public cloud (AWS, GCP, Azure) or on-prem Kubernetes cluster, contact us at info@sentrilite.com
Already installed? Get the credentials you need.
Free Token — required to log into the Sentrilite dashboard at port 8080 after a Docker install.
License Key — required for production deployments on public cloud or on-prem Kubernetes.
Request a New License Key
Request a Free One-time Token
Running the Sentrilite Docker dashboard? Enter your business email to receive a one-time login token by email. Public email providers (Gmail, Outlook, Yahoo, etc.) are not accepted.
Uninstall / Cleanup
docker stop sentrilite)
before running the uninstall command.
To cleanly unload all eBPF programs and remove Sentrilite from the host, run the following command. This executes the unload script inside a temporary container with the same privileges used during installation — no residual kernel objects are left behind.
sudo docker run --rm \ --privileged --pid=host \ -v /sys/fs/bpf:/sys/fs/bpf \ -v /sys/kernel/debug:/sys/kernel/debug \ --entrypoint /opt/sentrilite/unload_bpf.sh \ sentrilite/local:1.0.0