Cloud Cost Intelligence, Runtime Security & Vulnerability Assessment —
All in a single platform.
- ✓Cost Intelligence: Service-level cost breakdown. No manual pod tagging. Fully automatic. Start saving on Cloud Spend in minutes!
- ✓Runtime Security: Detect and prevent threats in real-time.
- ✓Vulnerability Assessment: Check your cloud security posture in minutes.
- ✓One command to install. One click for reports.
- ✓Lightweight — Minimal overhead. No sidecars. No code changes. Up and running in minutes.
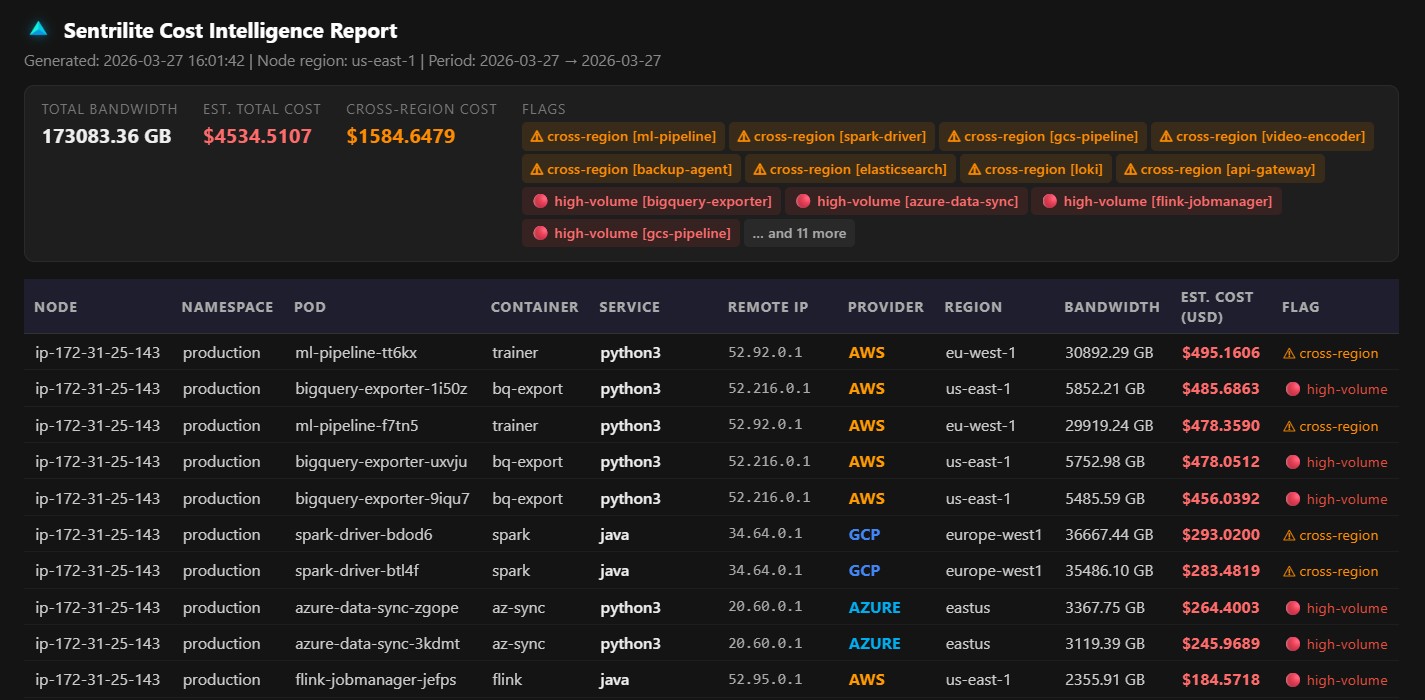
Cost Intelligence Report
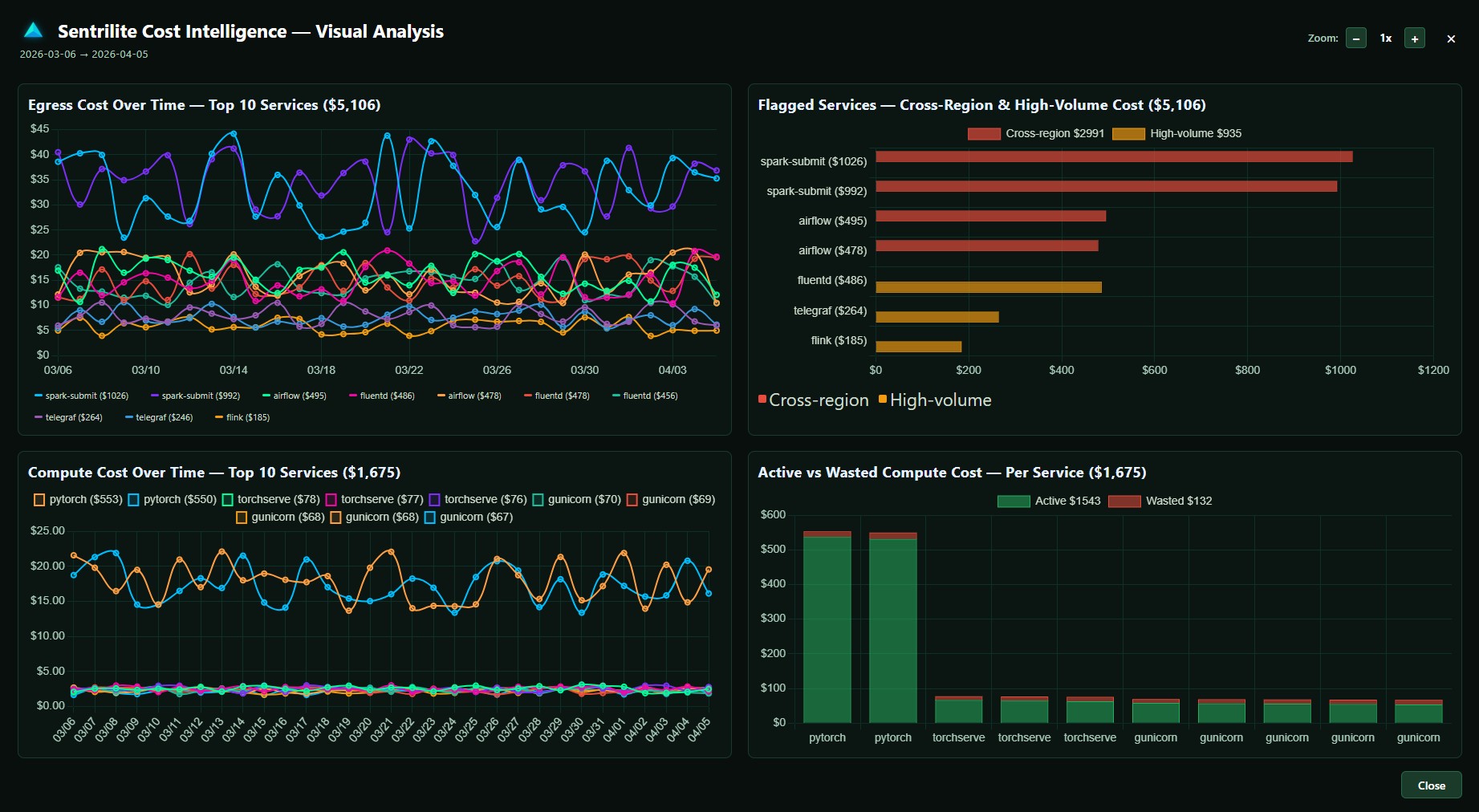
Visual Cost Analysis
Sentrilite vs. Others
How we compare on cost intelligence and security — across every dimension that matters.
| Capability | Sentrilite | Others |
|---|---|---|
| Cloud Cost Intelligence | ||
| Cost Attribution Granularity | ✓ Service-level cost breakdown using low-level kernel data — see exactly which process is spending what | ✗ Pod-level only — no visibility below the container boundary |
| Tagging & Instrumentation | ✓ Zero manual tagging — automatically maps services to compute and network costs from kernel events | ✗ Relies on kube metrics, Prometheus, or manual cost allocation tags — adds overhead and gaps |
| Runtime Security & Vulnerability | ||
| Zero-Day Protection | ✓ Kernel-level behavioural detection catches zero-day attacks that bypass signature-based tools | ✗ Signature-based detection only — no coverage for novel or unknown threats |
| Agent Footprint | ✓ Lightweight eBPF agent — minimal CPU and memory overhead, no sidecars | ✗ Heavy agents with significant resource overhead and complex dependencies |
| Setup & Install | ✓ One Docker command or Helm chart — running in under 5 minutes | ✗ Complex multi-step setup requiring dedicated ops time and ongoing maintenance |
| Alert Quality | ✓ Clean, risk-based alerts — prioritised by severity so teams focus on what matters | ✗ High alert volume with frequent false positives — leads to alert fatigue |
| Detection Rules | ✓ Fully customizable Detection-As-Code — write rules in plain JSON for your specific environment | ✗ Rigid, vendor-defined rulesets with limited customisation options |
| Detection Speed | ✓ Real-time detection and response — threats caught at the syscall level as they happen | ✗ Periodic polling or delayed ingestion pipelines — minutes to hours of lag |
| Pricing Model | ✓ Custom pricing tailored to your environment — no seat fees, no data ingestion charges, no surprises | ✗ Usage-based or seat-based pricing that scales unpredictably with infrastructure growth |
Capabilities that go deeper than any other cost or security tool on the market.
Process-level cost attribution
Attribution goes below the container boundary to the exact service and process making each cloud API call. Other tools stop at pod-level. We don't.
One-click cost intelligence report
Generate a full PDF cost intelligence report in one click — egress attribution, compute waste, cross-region flags, and anomaly detection. Ready for engineering or finance review.
Zero manual tagging
No cost allocation tags to maintain, no label enforcement policies, no untagged spend blind spots. Attribution comes directly from the kernel — 100% complete from day one.
Kernel-level vulnerability assessment
Scans for misconfigured services, exposed credentials, insecure file permissions, open ports, unauthorized kernel modules, and suspicious processes — from the kernel up.
Runtime security & zero-day prevention
Detects privilege escalation, namespace escapes, process masquerade, shell spawns, and lateral movement in real time — before they become incidents.
Works everywhere Linux runs
EKS, AKS, GKE, bare metal, VMs, hybrid on-prem — all in the same report. No Helm chart required for bare metal. No sidecar, no Prometheus dependency.
24×7 support
Direct access to the engineering team. Fast response SLAs, proactive alerts on new threat patterns, and guidance on optimizing your cost and security posture.
Latest threat research
Regular threat intelligence reports with new kernel-level attack patterns, CVE analysis, and cloud cost anomaly research from the Sentrilite security team.
Start free. Scale when you're ready.
Single node is free forever. No credit card required. No time limit.
