Agentic AI Governance across your infrastructure. Automatic Shadow AI Detection. No code changes. No proxies. No SDKs.
Tagless Cloud Cost Intelligence across AWS, GCP, and Azure. No tagging. No API credentials.
One agent. One command to install. One click for report.
OR
Explore the full platform in your browser.
Key Features
- Agentic AI Governance & Shadow AI Detection — Real-time visibility into every AI service your infrastructure talks to, with alerts on unsanctioned providers. No agents in your apps, no proxies.
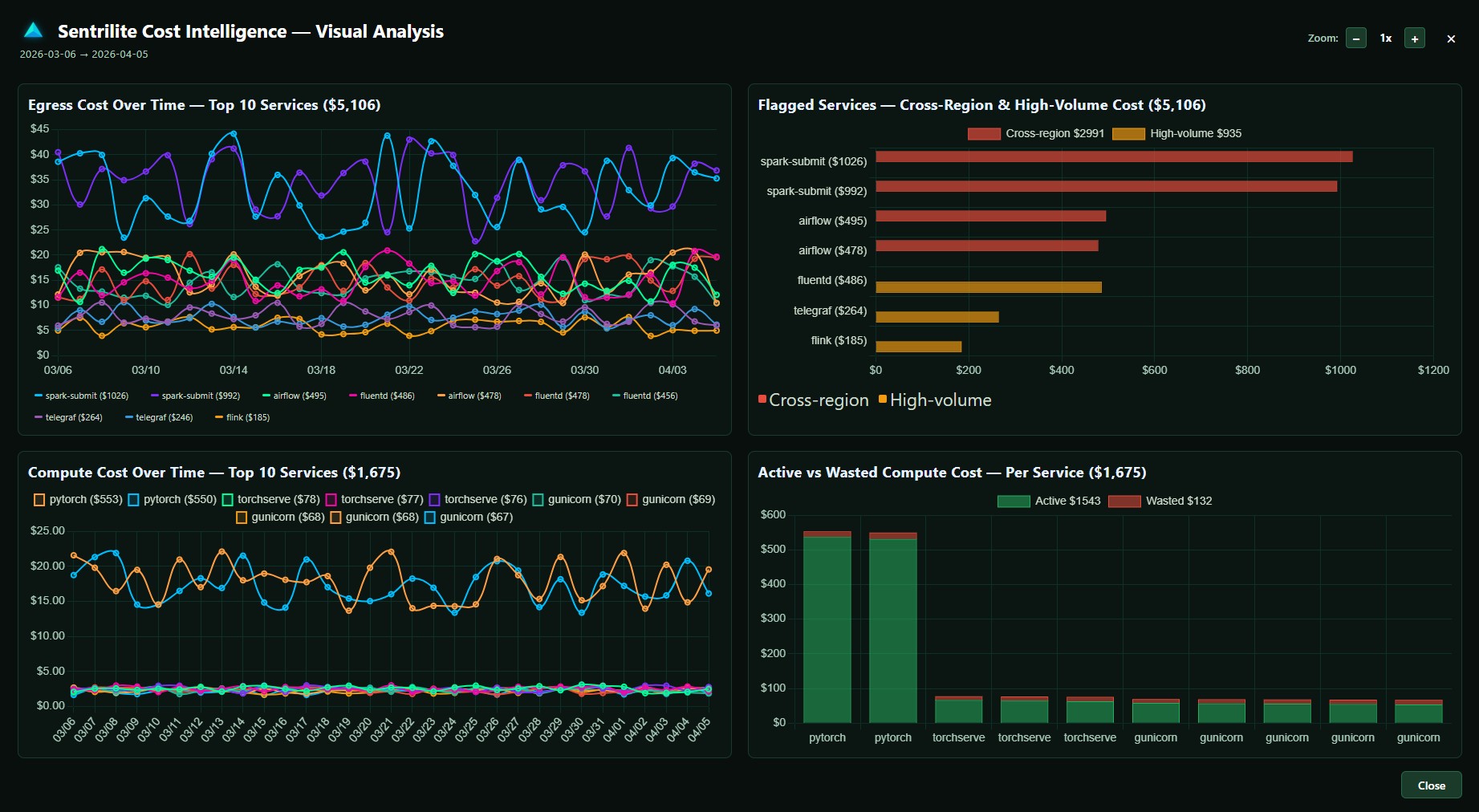
- Tagless Cloud Cost Intelligence — Real-time egress/compute attribution across AWS, GCP, and Azure. Drill down from Namespace → Pod → Container → Process → Cost.
- Runtime Security — Detect and prevent threats in real-time using easy-to-customize detection rules. Your infra → Your rules!
- Vulnerability Assessment — Scan your entire Kubernetes and hybrid-cloud infrastructure for misconfigurations, exposed credentials, and privilege escalation risks.
- One-Click PDF Reports — Generate audit-ready Cost Intelligence, AI Governance, Runtime Security, and Vulnerability Assessment reports instantly — with full context and remediation details.
How Sentrilite Works
1. Deploy in Minutes
Install as a Kubernetes DaemonSet (EKS, AKS, GKE) or run the lightweight Docker agent on any Linux host.
2. Real-Time Server Dashboard
Monitor system calls, file access events, and network connections in real time for every node in your infrastructure.
3. Centralized Cluster Overview
Track server health, alert status, and node groups from a unified dashboard with AI-powered insights for critical incidents.
4. One-Click Audit Reports
Generate structured compliance reports for any node group with a single click — ready for executive review and regulatory audits.
Schedule a Demo
Contact Us
Interested in learning more? Drop us a message at info@sentrilite.com — we'd love to hear from you.